This is the fourth in a series of articles analyzing the 27-page federal grand jury indictment charging lawyer Michael Sussmann with making a false statement to the FBI. Previous articles discussed the indictment’s detailed factual averments regarding how, during the 2016 presidential election campaign, Sussmann and others conspired to concoct a false but “plausible” narrative purportedly demonstrating the existence of a secret channel of internet communications between the Trump Organization, owned by Donald Trump, and the Russian Alfa Bank.
The indictment avers that Sussmann presented the false narrative to the FBI which then opened an investigation and that the conspirators used the false narrative and the fact of the FBI’s investigation to smear Donald Trump as an undercover Russian agent.
The indictment also avers that “[i]n or about April 2016, the Democratic National Committee (“DNC”) retained Sussmann to represent it in connection with the hacking of its email servers by the Russian government. In connection with his representation of the DNC as the victim of the hack, the defendant met and communicated regularly with the FBI, the DOJ, and other U.S. government agencies. In or around the same time period, Sussmann was also advising the Clinton Campaign in connection with cybersecurity issues.”
So what is the significance of that averment and why was it included in Sussmann’s false statement indictment?
Consider the following timeline of events:
On or about April 30, 2016, CrowdStrike, a California-based private cybersecurity company headed by former FBI official Shawn Henry, was retained by Sussmann to investigate the purported hack of the DNC’s email server.
On June 15, 2016, CrowdStrike announced that it had detected Russian malware on the DNC’s server.
The next day, a self-described Romanian hacker, Guccifer 2.0, claimed he was a WikiLeaks source and had hacked the DNC’s server. He then posted online DNC computer files that contained metadata that indicated Russian involvement in the hack.
On July 5, 2016, FBI Director James Comey publicly cleared Hillary Clinton of criminal charges for storing, sending and receiving “very sensitive, highly classified information” on her unclassified, private email server.
On July 22, 2016, just days before the Democratic National Convention, WikiLeaks published approximately 20,000 DNC emails.
Much to the embarrassment of Hillary Clinton, the released files showed that the DNC had secretly collaborated with her campaign to promote her candidacy for the Democratic presidential nomination over that of Bernie Sanders. This caused the Clinton campaign serious political damage at the Democratic convention.
Well after the convention, Jennifer Palmieri, Clinton’s public relations chief, said in a Washington Post essay that she worked assiduously during the nominating convention to “get the press to focus on … the prospect that Russia had not only hacked and stolen emails from the DNC, but that it had done so to help Donald Trump and hurt Hillary.”
On July 28, 2016, CIA Director John Brennan briefed President Obama on an alleged plan by Hillary Clinton to tie Trump to Russia as “a means of distracting the public from her use of a private email server” ahead of the upcoming presidential election.
Brennan’s handwritten notes (which were not declassified until 2020) state, in part, the following:
We’re getting additional insight into Russian activities from [REDACTED]…CITE [summarizing] alleged approved by Hillary Clinton a proposal from one of her foreign policy advisers to vilify Donald Trump by stirring up a scandal claiming interference by the Russian security service.
Similarly, on September 7, 2016, U.S. intelligence officials made an “investigative referral” to FBI Director James Comey on Hillary Clinton for allegedly approving “a plan concerning U.S. presidential candidate Donald Trump and Russian hackers hampering U.S. elections” in order to distract voters from her email scandal.
Nothing ever came of this referral.
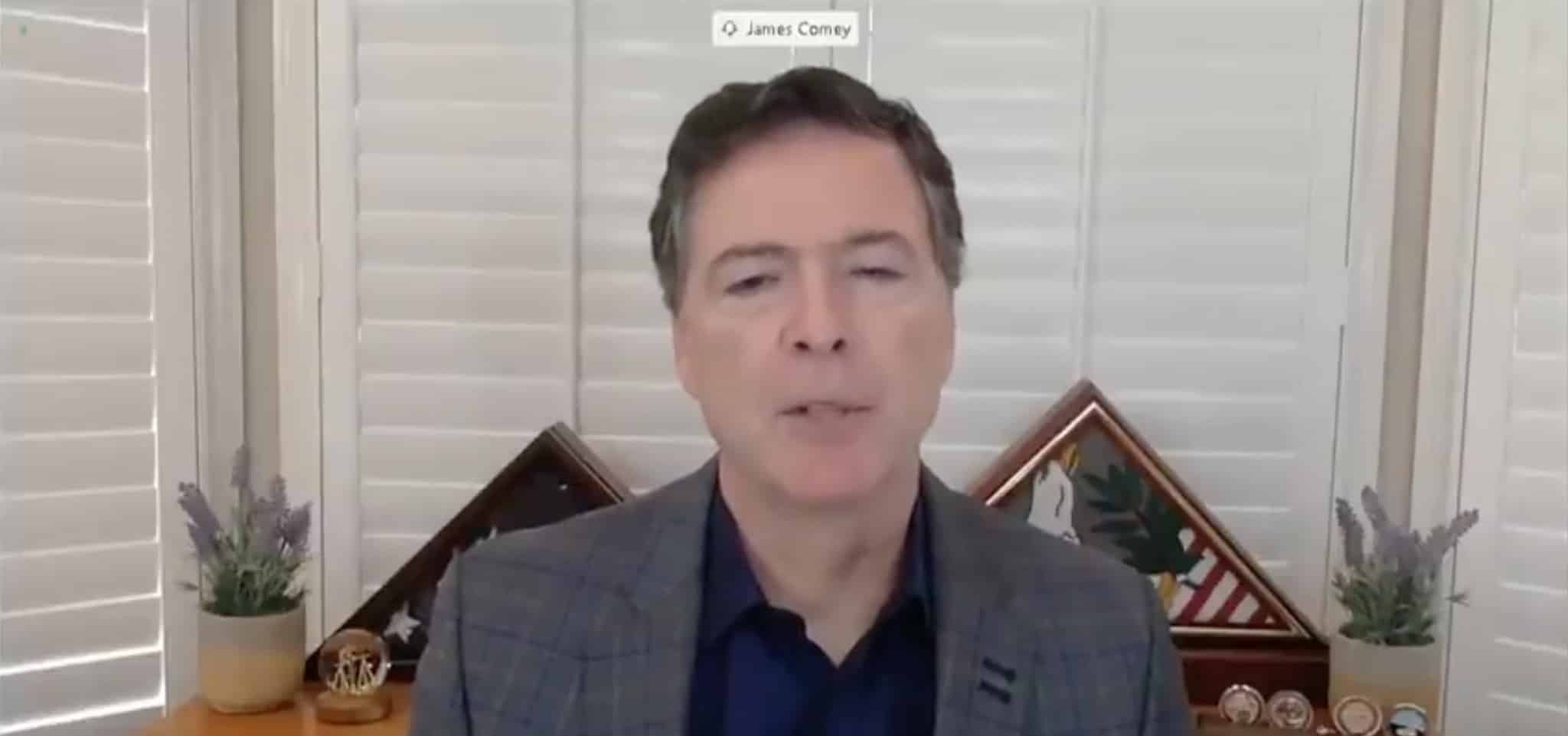
During a 2020 hearing before the Senate Judiciary Committee, when asked about the referral on Clinton, Comey said it didn’t “ring any bells.”
“You don’t remember getting an investigatory lead from the intelligence community? September 7, 2016, U.S. intelligence officials forwarded an investigative referral to James Comey and [Peter] Strzok regarding Clinton’s approval of a plan [about] Trump … as a means of distraction?” Sen. Lindsey Graham (R-SC) asked Comey.
“That doesn’t ring any bells with me,” Comey replied.
“That’s a pretty stunning thing that it doesn’t ring a bell,” Graham said. “You get this inquiry from the intelligence community to look at the Clinton campaign trying to create a distraction, accusing Trump of being a Russian agent or a Russian stooge.”
Graham added, “How far-fetched is that?”
But enough about Comey. Let’s get back to the alleged hack of the DNC’s server. When the Department of Homeland Security and the FBI learned of the hacking claim, they asked to examine the server.
But the DNC refused.
Instead, the server was examined by CrowdStrike, the cybersecurity company retained by Sussmann. And Comey’s FBI made no effort to gain direct, hands-on access to the DNC server, the scene of the alleged cybercrime.
Why would the DNC, the purported victim of a crime, refuse to fully cooperate with law enforcement in solving that crime? Was it hiding something? Was it afraid the server’s contents would discredit the Russia-hacking story? Why, instead of full and complete cooperation with the FBI, was the DNC having CrowdStrike and Perkins Coie run the investigation and, in effect, filter and control the flow of information regarding the server’s contents to the FBI?
The answers to those questions began to emerge thanks to an article in the August 8, 2017 issue of the Nation. By no means a pro-Trump publication, the Nation published an exhaustive report about an exacting forensic investigation of the DNC hack by the Veteran Intelligence Professionals for Sanity (VIPS), an organization of former CIA, FBI, National Security Agency, and military intelligence officers, technical experts, and analysts.
In its analysis of the purported DNC hack, VIPS brought to bear the talents of more than a dozen experienced, well-credentialed experts, including William Binney, a former NSA technical director and cofounder of the NSA’s Signals Intelligence Automation Research Center; Edward Loomis, former NSA technical director for the Office of Signals Processing; and Skip Folden, a former IBM information technology manager as well as other computer-system designers, program architects, and analysts.
VIPS concluded that the DNC data were not hacked by the Russians or anyone else accessing the server over the internet. Instead, the data were downloaded by means of a thumb drive or similar portable storage device physically attached to the DNC server.
How was this determined? The time stamps contained in the released computer files’ metadata established that at 6:45 P.M. on July 5, 2016, 1,976 megabytes (not megabits) of data were downloaded from the DNC’s server. This took 87 seconds, which means the transfer rate was 22.7 megabytes per second, a speed, according to VIPS, that “is much faster than what is physically possible with a hack.” Such a speed could be accomplished only by direct connection of a portable storage device to the server. Accordingly, VIPS concluded that the DNC data theft was an inside job by someone with physical access to the server.
VIPS also found that, if there had been a hack, the NSA would have a record of it that could quickly be retrieved and produced. But no such evidence has been forthcoming. Can this be because no hack occurred?
VIPS also determined that the files published by Guccifer 2.0 on June 16, 2016, had been “run, via ordinary cut and paste, through a template that effectively immersed them in what could plausibly be cast as Russian fingerprints.” In other words, the files were deliberately altered to give the false impression that they were hacked by Russian agents.
Thanks to the VIPS experts, the Russia-hacking claim — the very prologue of the Trump-Russia conspiracy story — appeared to have been affirmatively and convincingly undercut.
Moreover, even before VIPS’s findings were published, Wikileaks’ Julian Assange repeatedly denied that Russia “or any state actor” was the source of the stolen DNC data his organization published. And his denials later received confirmation in the March 5, 2018 edition of the New Yorker which featured a lengthy and sympathetic portrayal of Christopher Steele, the former British intelligence operative who was employed by Fusion GPS — yet another entity retained by Perkins Coie — to investigate possible connections between Donald Trump and Russia.
Buried toward the end of the article comes the revelation that, on July 26, 2016 (four days after WikiLeaks published the DNC emails), “Steele filed yet another memo” in which “Steele’s sources claimed that the [DNC] digital attack involved agents ‘within the Democratic Party structure itself…’” (Emphasis added.)
The Russian hacking narrative further unraveled on December 5, 2017, in an executive session of the House Permanent Select Committee on Intelligence (“HPSCI”). It was then that Shawn Henry, president of CrowdStrike, testified under oath that his company’s contract was not with the DNC but “with Michael Sussmann from Perkins Coie.” (Emphasis added.)
Consequently, CrowdStrike’s findings were protected by the attorney-client privilege, an argument raised during the HPSCI proceedings by an attorney from Perkins Coie. As he explained to the HPSCI, CrowdStrike was working for Perkins Coie and was “performing work in order to help Perkins Coie advise the DNC on this matter.”
Therefore, it was up to Perkins Coie and the DNC to decide what information CrowdStrike would be allowed to share with the HPSCI.
So what did Perkins Coie and the DNC allow Henry to tell the HPSCI about CrowdStrike’s findings?
That will be the topic of the next article in this series.
Stay tuned.
George Parry is a former federal and state prosecutor who blogs at knowledegeisgood.net. He may be reached by email at [email protected].